Thousands of articles try to explain what the Deep Web is. Most of them provide examples based on the different parts of an iceberg, which is divided into levels each of them containing some kind of information. How do these levels increase encryption proportionally to their depth? And, even more important, how does the content hosted increases its savagery and emotional impact as it gets closer to the bottom. All of this is based on the well-known iceberg theory.
Without wishing to challenge their authors or calling these comparisons into question (lots of them made by subject matter experts), not everything that you find in the Deep Web has to be illegal or has to have glimpses of depravity. Naturally, the first thing that comes to our minds is the content related to pornography, mainly child pornography, arms trafficking, trafficking in human beings, drugs and any other activity taking place not only outside the law but very far from it. However, the Deep Web is more than all that. For example, create a PowerPoint document on your block of flats, including the number of floors, the number of flats on each floor, the colour of the doors, the number of parking spaces, etc. Protect such ‘sensitive’ information with a password and upload it to your blog ‘Charming Houses’. This presentation, particularly its content, will be part of the Deep Web. Why?
Sometimes, when trying to explain what something is, it is better to shed some light on what it is not. This time, we have resorted to the experts of the Cybercrime Group of the Civil Guard, or Grupo de Delitos Telemáticos (GDT), who have not hesitated to guide us in looking for answers. In fact, it was their idea to avoid trying to explain, first of all, what the Deep Web is, but to start by explaining what the visible part is, the tip of the iceberg, if we continue with this metaphor, i.e. the part that we can see at home, at work, on our Smartphone while having a coffee or travelling on the bus.
DEEP WEB VS VISIBLE WEB. As the saying goes, you cannot try to stem the tide, but can Internet be stemmed? More pending questions. In order to differentiate Deep Web from visible web we need to refer to the term ‘to index’ –to sort data or information following a common criterion in order to make consultation and analysis easier -.
Because this is what the search engines do: they index. If we use the biggest search engine, Google, as the subject of our work, we will see that this engine is not searching the word/s of our consultation in real time nor in every server in the world. That would be impossible.
The system regularly sweeps the accessible sites and indexes them, creating an index on the database of the search engine that we use. If we type in ‘cheap flats in Soria’, apart from the more than 500,000 results, the browser’s bar will show https://www.google.es/search?q=indexar&ie=utf-8&oe=utf-8&client=firefoxb&gfe_rd=cr&ei=LoOGVmXF4rY8geazYHwCg#q=piso+baratos+en+soria.
The term ‘index’ is part of it, this is the order sent by Google to its browsers in order to look up in all the sites that contained the words that we are searching: Cheap/flats/in/Soria. This is the visible part, the part that shows in our consultations. And here is where we ‘stem the tide’.
The rest is Deep Web, or in other words, everything that you cannot find in a more or less easy way, that is Deep Web. Our PowerPoint presentation will be part of this invisible internet, not the presentation as such which will be easy to find, but the content, as it is protected with a password. How to avoid the protection, that’s another story.
Let’s explain this with a more glaring example: the username and password that the insurance company sends us to manage the products that we have contracted. This process and information cannot be indexed by the search engines; this is part of the Deep Web.
Based on that, when the GDT officers are asked about the Deep Web they emphasize two main aspects: first, not all the content that cannot be indexed has to be illegal and that Internet is not only Google or other search engines.
Let’s think of Internet as a town made up of streets and these made up of houses. What you do in your house, out of Google’s reach (or any other search engine) does not have to be bad. It is part of your private life. Naturally, if you want to set up an amphetamines lab (in the style of Breaking Bad) you will not set it up at the Town Hall square; instead you will implement all the necessary measures to shield it from prying eyes. But, how to escape from these prying eyes? What can this anonymity provide you? Not only for committing a crime, but, for example, also, for hosting relevant information regarding the company you work for and that you try to protect from industrial espionage.
TOR NETWORK, ANONYMITY GUARANTEED. Within the Deep Web concept there are encrypted anonymisation networks, like TOR or Freenet, that they are nevertheless services offered by Internet to surf the net anonymously. But, is wishing to keep anonymous illegal? Obviously, not.
Without going into technical detail, the TOR network, which stands for ‘The Onion Router’, is a parallel communication network that has a high level of anonymity. Naturally, lots of the users of this type of network resort to this service to commit a crime. Only amateurs would set up a drug sales business on a web to which you can have access using the traditional search engine. However, there are people who need this type of anonymity for personal safety reasons. But, how do you achieve anonymity? Well, we will refer to its name to explain it: Onion. We can draw a parallel with the layers of the onion and the TOR users. This network employs its users in the information exchange in such a way that the information jumps from one user to the other, wrapping the message in a new layer of the onion, which will make it very difficult to obtain information if you are an outsider. Also, each incorporation of a layer represents an encryption of the message. The way back from the server to the source user follows the same protocol, so it is impossible to identify those involved in the operation.
The TOR network would be twofold: it would be used by those who wish to provide an illegal service, but cannot advertise it like a shop, and by those with a legal purpose who wish to anonymise their connection, either because they are paranoid thinking that they are being monitored, or something more usual that takes place in countries where fundamental rights are limited and where to share information reporting abuse by the Government becomes a real danger. The great value of TOR is the difficulty to detect where the web page is hosted or who is a user or who has installed it.
Not all the content that cannot be indexed has to be illegal
The officers of the Cybercrime Group think that the TOR functions are more useful for those who plan to commit a crime and also underline that you will find more traps and barriers than in the visible part. As TOR is so vilified, we will be subject to any type of coercion or extortion just for logging in and it will be assumed that the TOR user is searching something illegal just because he or she is using TOR. But, it is illegal to use TOR in Spain? No, but is it illegal in those countries where fundamental rights are limited, for the reasons explained above.
THE GDT, TOR AND ILLEGAL ACTIVITIES ON THE WEB. Given the vast amount of information and encryptions, the investigation of these crimes becomes a complex one. On many occasions, the process to detect illicit activities involves international cooperation. In police jargon, when a server is ‘taken down’ the entire users database is compartmentalised in order to identify the country that could be interested in the information and share it. Globalization travels in all directions. Statistics reveal how most operations against TOR usually are the result of international information exchange.
However, the officers of the GDT admit that most countries have unfinished business: prevention through Internet, i.e. staff continuously engaged in tracking illicit behaviour in private networks like TOR. Human resources of police forces are limited. In fact, the crime involving fraud and other criminal activities that use Internet require such an amount of human and material resources that there are hardly any resources left to be devoted to surf in the TOR network. The investigators find other burdens when developing an operation. The first one is to know where the page under investigation is located, as the investigators are only empowered to investigate the crimes committed in Spain or by Spaniards. They also have to face the silence of the victims in these types of crimes. Obviously, no one wants bad publicity. And that is the essence of the problem. Big companies that are victims of fraud or scam prefer to accept the fraud and hide it. And this is a big burden for the investigation.
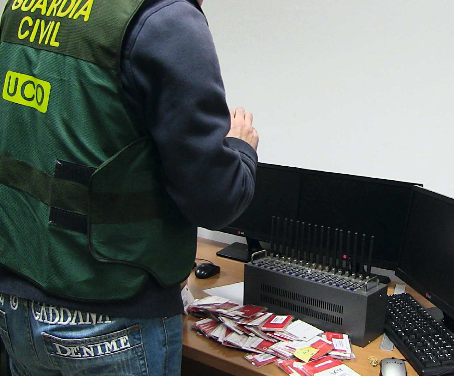
One of the main features of the GDT is their determination to improve and better themselves. GDT and J-CAT. One of the main features of the GDT is their determination to improve and better themselves. This is why since its creation in 1996 within the Central Operational Unit (UCO) as Computer Crime Group until today, they have not only changed their name, but also their organisational and functional distribution.
According to one of the GDT officers, ‘if the investigator cannot adapt to evolution he or she will be sunk’. Obviously they are not sunk. They strive to find cybercriminals and that is why they keep on updating their knowledge and they regularly attend forums, courses and conferences, not only as attendees but also as speakers. Probably, that required evolution leads them to be a Unit open to all the Civil Guard officers. Their doors are always open to any member of the force that wishes to collaborate with the Group, as a member –if the joining requirements are met – or collaborating from home. Given that nowadays all of us surf the web to a greater or lesser extent, and any useful information that we obtain can be forwarded to the Group, so we will be external collaborators. ‘We need eyes and ears everywhere, much better if they belong to the Civil Guard’ as the GDT officers state.
As pointed out before, international police cooperation is fundamental to stop cybercrime, that is why the GDT maintains constant communication with foreign police forces, either directly or through Interpol or Europol. Within this latter agency an active working group has been created to fight cybercrime. The group, called Joint Cybercrime Action Task Force (J-CAT) and based in The Hague (The Netherlands), is composed of police officers from European and American police forces that work together and have direct communication.
Spain, Germany, USA or Canada are represented in this platform. Any type of information or collaboration needed by a country regarding cybercrime can be requested and answered immediately, thus achieving an enhanced operability. This effectiveness is demonstrated by the huge number of operations that take place and result in the arrest of cybercriminals in different countries simultaneously.
By Diego l. Cantos and Santiago Suárez, Guardia Civil.